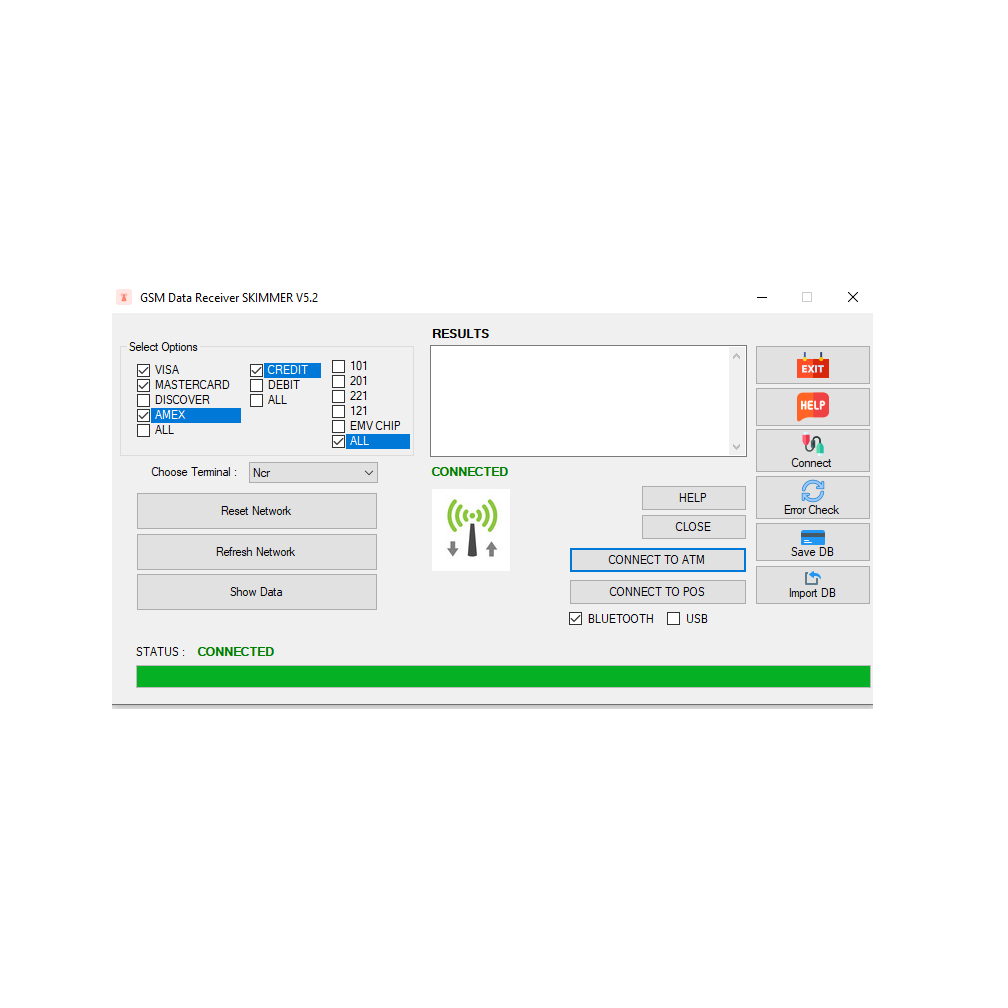
Gsm data receiver skimmers official vendor
Advanced GSM skimming devices with real-time data transmission capabilities. Professional-grade equipment for seamless card data acquisition
Installation & Setup
Deploy our GSM skimmers effortlessly. The device requires minimal technical expertise for discreet placement and activation. Its compact design ensures covert operation, allowing for rapid deployment in various environments without detection. Simply power on, position, and begin passive data acquisition.
Real-Time Data Capture
Access intercepted credit card data instantly. Our skimmers provide immediate transmission of captured track 1 and track 2 data as transactions occur. This real-time capability allows for rapid assessment and exploitation of compromised financial information, ensuring maximum operational efficiency and minimizing exposure.
Data Extraction & Card Cloning
Securely retrieve and replicate stolen card data. Captured financial information is stored encrypted and can be downloaded via a secure interface. Utilize the extracted data to format new magnetic stripe cards, creating fully functional clones for immediate use. This process is seamless, enabling swift monetization of acquired assets.